Hackers can get into anything these days – even the car sitting in your driveway. A new cybersecurity report from Upstream Security highlights the growing problem of car hacking in their annual report. And they’re warning you to be prepared for increased threats. A lot more.
According to the tech firm based in Israel, there has been a 99 percent increase in cybersecurity incidents (to 150) in 2019 and a 94 percent year-over-year increase since 2016 related to cars.
And with more communication methods and external connections being built into new vehicles, including massive over-the-air update technologies, this trend is likely to continue exponentially well into the future.
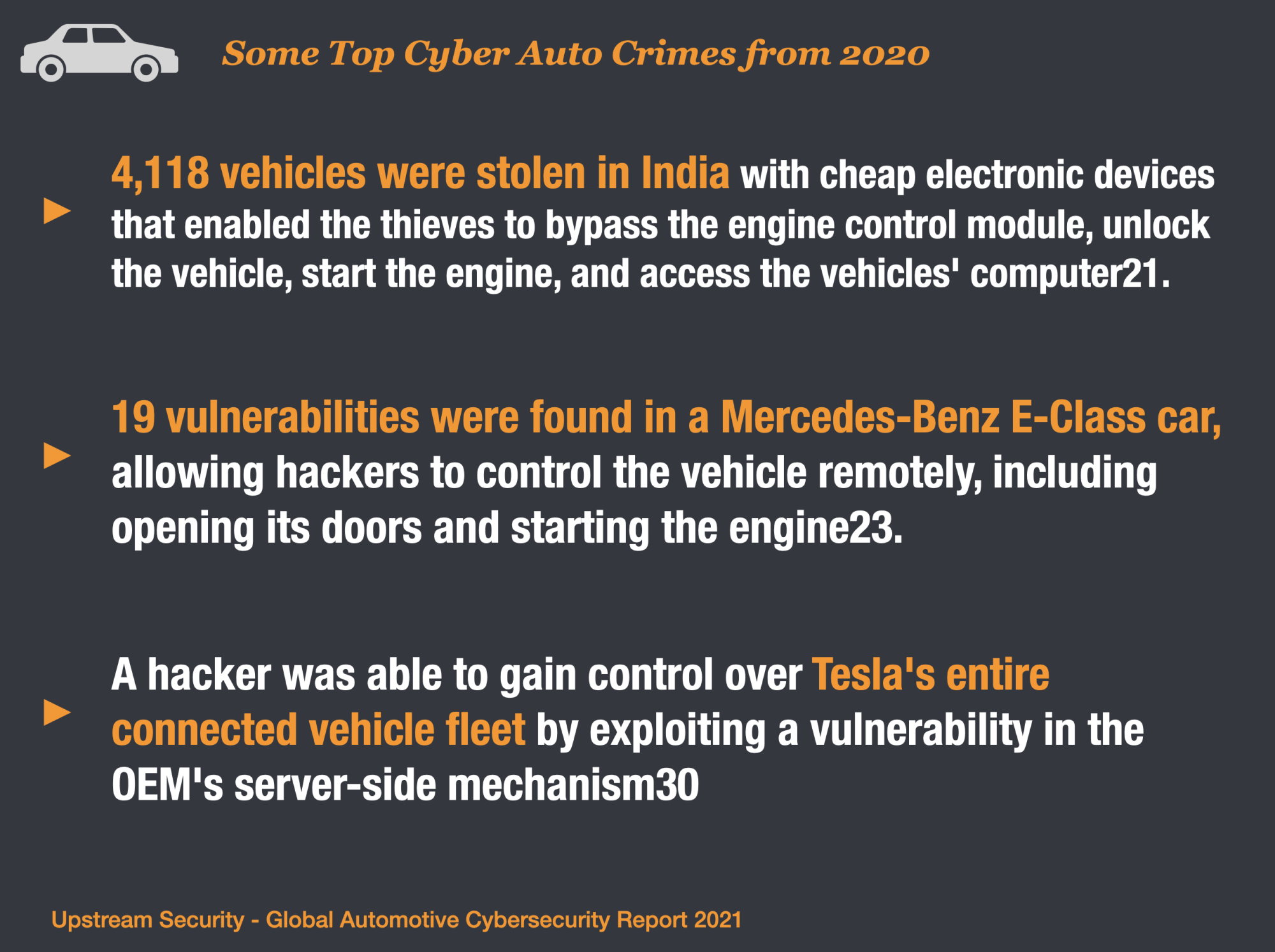
Top CyberCrime Events Involving Autos in 2020
Upstream analyzed 633 publically released cybercrime events since 2010. 1/3rd of those events took place in 2020.
3 of the top Cyber Auto Crimes included:
FOB-related CyberCrime in India – 4,118 vehicles were stolen in India with cheap electronic devices that enabled the thieves to bypass the engine control module, unlock the vehicle, start the engine, and access the vehicles’ computer21.
Mercedes Benz Vulnerabilities – 19 vulnerabilities were found in a Mercedes-Benz E-Class car, allowing hackers to control the vehicle remotely, including opening its doors and starting the engine23.
Tesla Fleet Comandeered – A hacker was able to gain control over Tesla’s entire connected vehicle fleet by exploiting a vulnerability in the OEM’s server-side mechanism30
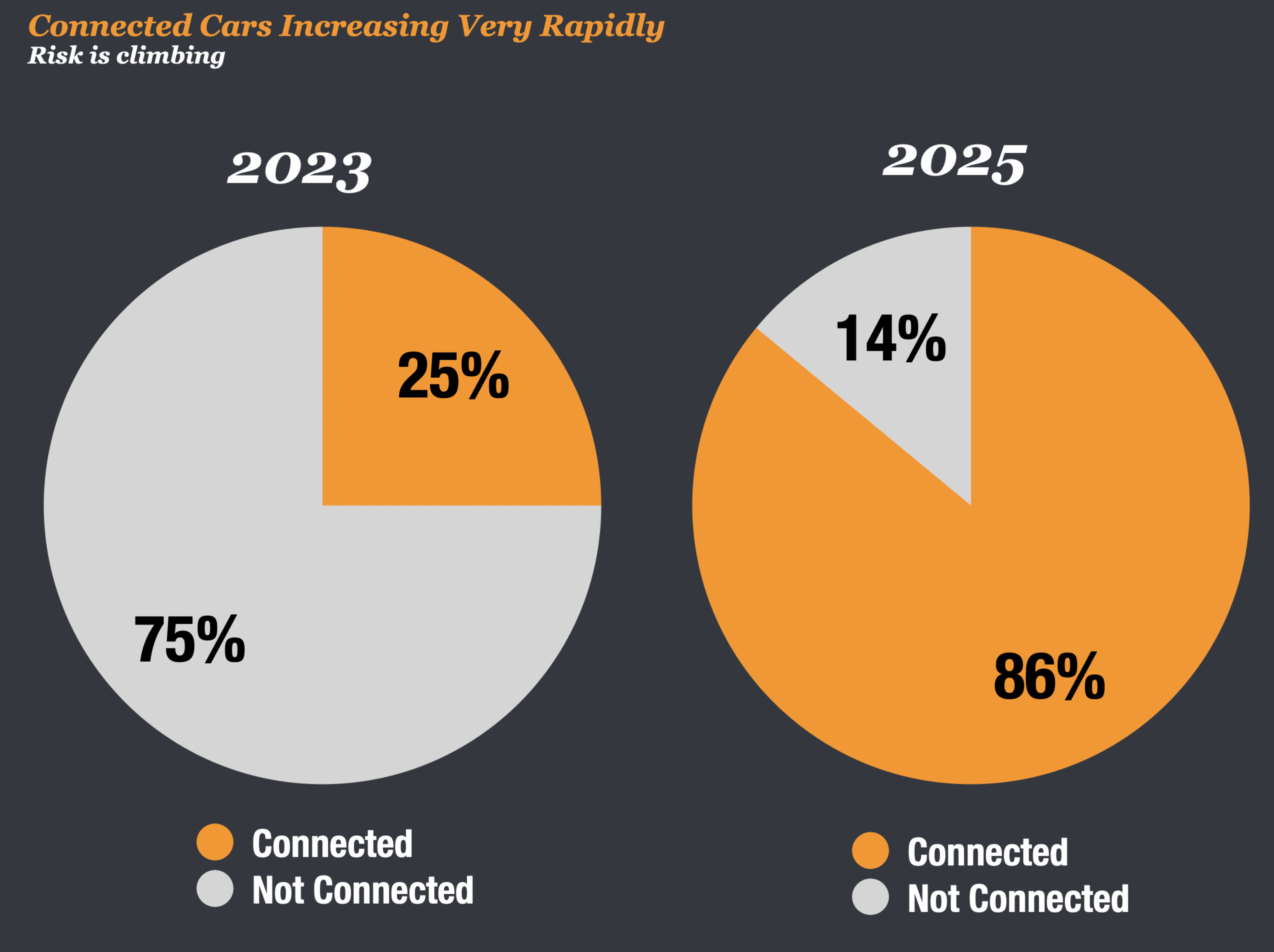
Connected Vehicles Will Be The Norm
In 4 years, most cars will be connected to the internet. That is great. But it’s going to come with its own share of headaches.
The growth in connected vehicles is going to drive exponential increases in cybersecurity risk. According to Upstream, by 2023, 25% of vehicles worldwide will be connected. By 2025, that number will jump to over 86%.
And those connected vehicles will be far more sophisticated and have more features that can be controlled remotely than when connected autos were first launched by GM back in 1996.
That means that if hackers can get into your car, they can do far more damage than anyone could have ever imagined.
They Can Control Your Steering and Breaks, Even Shut Down Your Engine If They Want
The more sophisticated the car, the more that hackers can do with your car. You might be surprised by just how much they can do.
Moshe Shlisel, the CEO and co-founder of GuardKnox Cyber Technologies told the Detroit Free Press recently that new cars are highly subject to digital intrusion. And he knows this because they employ white hat hackers that test the system.
“We have taken whatever model [car] you think of and we hack them through various places. I can control your steering, I can shut down and [start] your engine, control your brakes, your doors, your wipers, open and close your trunk.”
With all of these vulnerability car manufacturers are making sure they have their own teams of cyber experts to help plug the holes that exist in the technology.
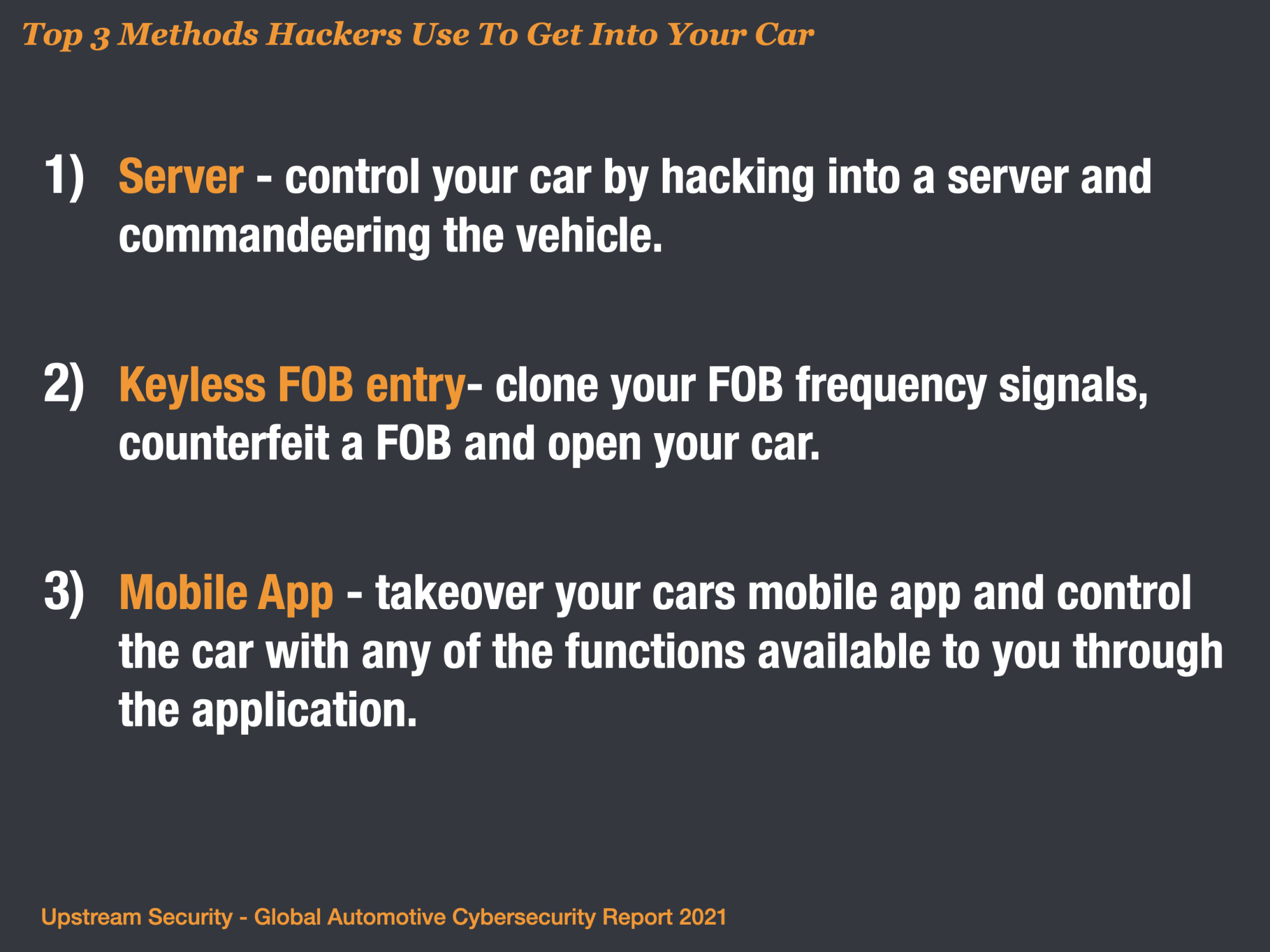
Here Are The Ways They Are Likely To Hack Your Car
Upstream identified the most common attack vectors since 2010 as part of their report. While there is a diverse list of attack vectors, the top 3 schemes Server hacking, Keyless FOB Entry, and Mobile App Takeover accounted for well over 70% of the historic risk.
The full list of ways hackers can exploit your car:
- Server Attacks
- Keyless Entry
- Mobile App
- OBD Port
- Infotainment
- IT Network
- Sensors
- ECU/TCU/GW
- In Vehicle Network
- WIFI
- Bluetooth
- OBD Dongle
- Cellular Network
- USB Port
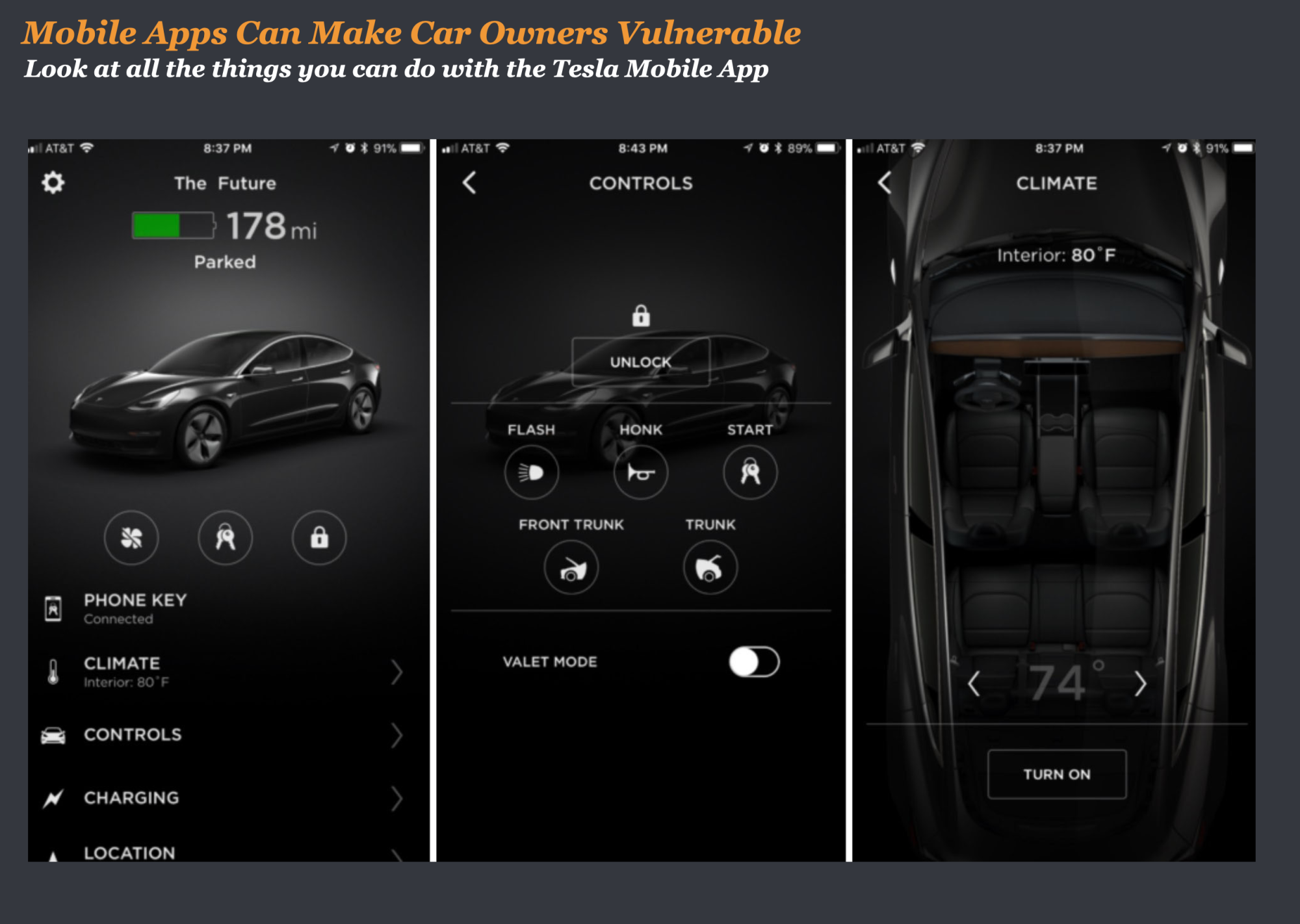
Mobile Applications Offer Convenience, And Risks
Mobile apps are becoming ubiquitous. This is particularly true in commercial fleets. According to Upstream, “At least 90% of truck drivers today carry a mobile device with a tracking app, and most large fleets have invested heavily in mobile apps to enhance their services.”
And the growth in cars connected via mobile apps is on a tear. In August of 2020, Google announced that their app Android Auto would soon be available on over 100 million cars.
But the apps are particularly vulnerable to hacking. As an example, Upstream reported that “In August 2020, a car owner in China discovered a bug in Tesla’s app which displayed five cars in Europe instead of his own car. He was able to view the information of each car and even remotely control them as if he owned them.”
The Future is Bright, But Risky
So what does all this risk mean? Does it mean that we should steer clear of a future where cars are connected via apps, servers, and the internet?
The answer to that is obviously no, but we need to be aware of the risk and build in on cybersecurity and threat mitigation all throughout the process.
Great research by Upstream and I highly recommend you download the whitepaper here – Upstream CyberSecurity Report.



